2009 Recipients of C&C Prize
Group B

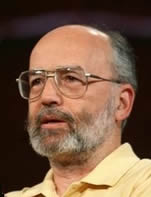
Prof. Ronald L. Rivest Andrew and Erna Viterbi Professor of Electrical Engineering and Computer Science |
Prof. Adi Shamir The Paul and Marlene Borman Professorial Chair of Applied Mathematics |

Prof. Leonard M. Adleman Henry Salvatori Chair in Computer Science and Distinguished Professor of Computer Science and Biological Sciences |
Citation
For the invention of the RSA algorithm for public-key cryptography
Achievement
Profs. Ronald L. Rivest, Adi Shamir, and Leonard M. Adleman invented a pragmatic algorithm for public-key cryptography in 1977 as researchers at the Massachusetts Institute of Technology. Using the initials of these three inventors, it was named the RSA algorithm. It takes advantage of computing difficulty in factoring large numbers.
The idea behind public-key cryptography is quite different from that of conventional symmetric-key cryptography, where the same key has to be used for encryption by the sender and decryption by the receiver. In public-key cryptography, the owner creates a pair of keys. One is used as a public key for encryption. The other is used as a private key for decryption. The encrypted data can only be decrypted by using the owner's private key.
In a practical RSA system, the public key and private key are created using two prime numbers having hundreds of digits. However, because only the product of the two prime numbers is disclosed, the prime numbers are virtually unidentifiable due to the difficulty of computing factorization into prime factors. This means that without knowledge of the owner's private key, it is almost impossible to decrypt within a viable timeframe even if the best currently known algorithms and the fastest computer systems are used.
Until the invention of public key cryptography, a symmetric (secret) key had to be exchanged in advance between the sender and receiver via a secure communication path. However, with the emergence of the RSA algorithm, a secure form of network communications was created in a practical manner and a secret key exchange is no longer required.
Another feature of public-key cryptography is that it is used for the generation and authentication of electronic signatures. It proves that a signed message originated from the owner. For the authentication, the owner sends the message and message-dependent data encrypted with a private key as a signed message. The receiver then decrypts the data with a public key. If the data is decrypted correctly, it proves that the owner sent the data. The Public Key Infrastructure (PKI) on the Internet based on the authentication technology developed with public-key cryptography has enjoyed widespread use in inter-business e-commerce, electronic application procedures in e-government, electronic document signing, user certifications, and others.
Thus, the invention of the RSA algorithm for public-key cryptography by Profs. Rivest, Shamir, and Adleman and their contributions to the progress of the IT security industry have received very strong international recognition.
